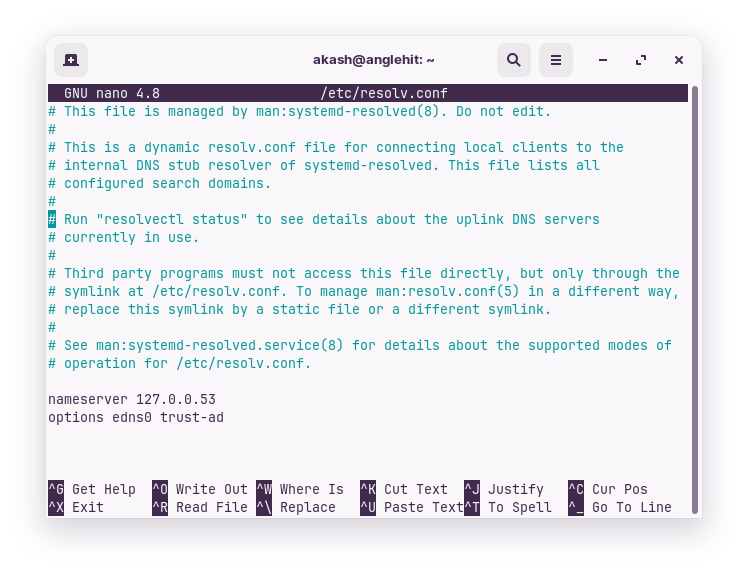
Editing resolv.conf wont give you internet access if you don’t already have it, but this edit can fix a very specific problem.
This file controls hostname resolution using DNS. If your computer is configured to use a DNS server (or is configured via DHCP or something) and that server is broken, then this helps.
#nameserver ::1
#nameserver 127.0.0.1
nameserver 8.8.8.8
nameserver 8.8.4.4
Specifically, the first two lines (which are commented out and disabled) use a local DNS server that is presumably configured to talk to an upstream DNS server.
The next two lines configure the system to instead use Google’s DNS servers (8.8.8.8 and 8.8.4.4). It is a matter of opinion (out of scope here and not enough info even if it wasn’t) if this makes your system less secure or more secure than whatever unknown default DNS servers your system would otherwise use.
Also note (as mentioned in the other more Ubuntu specific answer) that editing this file may disable automatic DNS network configuration and/or may be stepped on by automatic network configuration.
Further explanation as follows:
Editing the /etc/resolv.conf file to add DNS server information can be a temporary workaround to restore internet connectivity in certain situations.
However, it is not considered a secure or reliable long-term solution. Here’s why:
Dynamic DNS Configuration: In modern Ubuntu versions, including Ubuntu 22.04, the /etc/resolv.conf file is dynamically generated by the system based on network configuration settings. Modifying this file manually may lead to conflicts or being overwritten by network manager services, DHCP (Dynamic Host Configuration Protocol), or other network management tools.
Network Manager: Ubuntu uses Network Manager as the default network management tool, which dynamically manages network connections, including DNS configuration. Network Manager handles DNS resolution by utilizing the DNS server settings obtained from DHCP or other network configuration sources. By manually editing /etc/resolv.conf, you may interfere with Network Manager’s functionality and cause unexpected behavior.
Security Considerations: The /etc/resolv.conf file can contain sensitive information, such as DNS server addresses or search domains. By modifying it manually, you might introduce security risks or expose your system to potential attacks. Additionally, your changes might be lost or overwritten during system updates or network re-configurations.
To ensure secure and reliable DNS configuration in Ubuntu, it is recommended to use the standard network configuration tools provided by the operating system. Here are some alternatives:
Network Manager Configuration: Use the Network Manager GUI or command-line tools (e.g., nmcli) to configure DNS settings. This allows Network Manager to manage DNS configuration properly and ensure consistency.
systemd-resolved: Ubuntu 22.04 and newer versions utilize systemd-resolved as the DNS resolver by default. You can configure DNS settings using the systemd-resolve command or by modifying the appropriate configuration files under /etc/systemd/resolved.conf.d/.
DHCP Configuration: If you are obtaining network configuration information from a DHCP server, ensure that the DHCP server is correctly configured to provide the appropriate DNS server addresses. This way, your system will automatically receive the correct DNS settings without manual intervention.
By relying on the standard network configuration tools, you can ensure that your DNS configuration remains consistent, secure, and compatible with system updates and network management services.